The Weekly Distillation No.41
Cyber Warfare; Corporate Exploitation; Semiconductors; Employee Incentives; Money Supply; AI; Beer
Welcome to The Weekly Distillation. This is a newsletter that seeks to distill the noise and help you be informed, provoked to think, and inspired to create as you lead in life and in your organisation.
This week’s newsletter is sponsored by Fractal Brewing Project.
Fractal Brewing Project is a production brewery and taproom in Huntsville, Alabama. The brewery produces a wide range of beverages from traditional crisp lagers to boundary-pushing fruited sours to non-alcoholic craft root beer. The taproom serves a private event space room, spacious indoor tavern, and a large outdoor space with a covered patio. The elements that make up Fractal form a relaxed environment where both artist and engineer can unwind and explore new ideas together. With fractals, everything of interest happens at the boundaries - same with ideas and relationships.
Follow them @fractalbrewing on Instagram and Facebook.
I almost got to this brewery in 2019…but then my youngest son broke his arm on a slide at the Space & Rocket Center and that was that. A good friend built this business and I’m looking forward to visiting it one day soon.
People once said……..
“It’s like the embers in a barbecue pit” - Neil Hyatt, nuclear materials chemist at the University of Sheffield when talking about recent fission reactions at the Chernobyl Nuclear Power Plant in Ukraine
“SpaceX launching satellite Doge-1 to the moon next year – Mission paid for in Doge – 1st crypto in space – 1st meme in space To the mooooonnn!!” - Elon Musk
"I am grateful to the people of this constituency for their support. I never take a single vote for granted, and I am sincerely grateful for the trust placed in me by the people of Skye, Lochaber and Badenoch." - Kate Forbes, 31 year old Finance Minister of Scotland after taking 56% of the vote in her constituency
“Through Hamas, Iran has been able to buy itself a seat on the table in talking about the Palestinian issue. And, as a result, through Hamas it does play a role in the issue of the Palestinians, as strange as that should sound.” - King Abdullah II of Jordan
“If you’ve been fully vaccinated -you can resume activities that you did prior to the pandemic. You can resume activities without wearing a mask or staying 6 feet apart, except where required by federal, state, local, tribal, or territorial laws, rules, and regulations, including local business and workplace guidance.” - US Center for Disease Control
Skim it in a minute
Coinbase is simplifying how it attracts, rewards and incentivises its employees. Interesting changes on vesting in particular.
There’s a shortage of semiconductor chip manufacturing capacity. Here’s why we can’t just quickly fix that problem. Good job we don’t use those chips for much isn’t it. Oh no, that’s right……
We’re starting to train AI how to write its own instructions. Yes, teaching the computers to code by using GPT-3. I wonder if it would be a good idea to let my children read the whole of the web and then give them the power to code. That’s what we’re doing with GPT-3. At least my children have some morals.
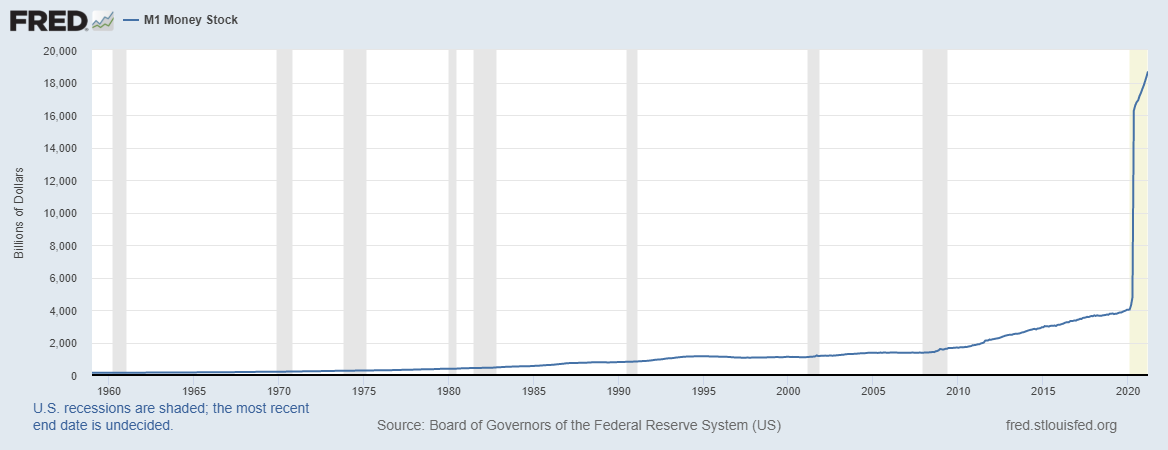
Not a quote but I came across these charts showing the amount of $ in circulation (money supply) this week. M2 is the best definition of money supply as it includes non-physical assets (i.e. money at a bank as opposed to notes and coins). M1 is notes and coins in circulation plus on demand deposits. The quantum of the increase in my lifetime is staggering (the axis is $bns).
A Deep Dive into Cyber War
Photo by Jefferson Santos on Unsplash
This week in the US, a ransomware attack on Colonial Pipeline, shut down 5,500 miles of pipes and caused fuel emergencies in four states. Also this week, the Irish Health service has come under attack and has had to close down its IT systems.

It makes big headline news - but is the threat significant, in what form do cyber attacks come and how can we prepare for them? I’m not a coder (I did Computer Science Higher at school and I was a technology equity research analyst for a US Investment Bank once) but I did study an online course in cyber warfare and cyber terrorism through the Handa Centre for the Study of Terrorism & Political Violence at the University of St Andrews a couple of years ago. This still leaves me completely unqualified but let me share some of what scared me in that studying.
Forms of Cyber Warfare
Spying
The simplest of all. Get in, steal the info, get out. Or get in, leave a (automatic) mole in place and have it keep feeding it back to you. Examples:
The NSA recording Angela Merkel
The Chinese accessing plans for the new F35 fighter jet via hacking into defence contractors in Australia
The Solarwinds attack by Russia
Sabotage
The physical or digital damage to property or assets of another entity through the execution of code. The part that seem so clever when done by your allies and potentially devastating when carried out against you. These can be DDoS (Distributed Denial of Service), ransomware (which could be a 4th category of financial theft but often leads to sabotage if not paid) or attacks against infrastructure (water, power, airports, railways, oil pipelines). Examples:
The Colonial Pipeline Attack
A 12 hour power blackout for 40m people in Turkey, caused by Iran
The Natanz attack by Israel and the Stuxnet by Israel & CIA, both targeting Iran’s nuclear weapons programme
The Wannacry ransomware attack on the UK’s National Health Service
The current Irish Health Service attack
Propaganda
Rightly or wrongly, propaganda by military forces has become a major part of cyberwarfare. From this week you have the IDF pushing out social media campaigns to influence Western cities and politicians:
Or from Russia in running active social campaigns to oppose Western policies:
 💬 #Zakharova: The #US 🇺🇸 explains the 9⃣5⃣th wave of anti-Russia sanctions alleging the @solarwinds software used by their government agencies was hacked. The US intelligence community is simply using a ❌ "false flag" for provocations to milk the government for more money.
💬 #Zakharova: The #US 🇺🇸 explains the 9⃣5⃣th wave of anti-Russia sanctions alleging the @solarwinds software used by their government agencies was hacked. The US intelligence community is simply using a ❌ "false flag" for provocations to milk the government for more money.
Neither of these are the extremes of propaganda and disinformation that can be spread. Terrorist groups are as active in this as nation states.
All 3 of these forms (propaganda, sabotage, espionage) are being carried out all of the time by multiple state, non-state and organised crime groups. It is believed that there are significant links between all 3 of those parties in the case of several nation states.
It is also worth noting that truth is thin on the ground in cyber warfare and it’s almost impossible for a non state actor to prove who did what. We need a Bellingcat for cyber attacks.
Does it matter to you?
Zero days - I recently bought a book called “This is how they tell me the world ends” (a great title) - a book all about Zero Day cyber weapons by Nicole Perloth of the NY Times. A zero day bug is one that exists in the code in a mobile app, a piece of software, your phone, an internet connected camera etc and has been discovered. It is called zero day because there has been zero days to fix it. These bugs are doorways into code, that can enable a malicious party to enter and linger, watch, leave a logic bomb to be triggered later or at a specific time, or to steal money or data. There is an active market in zero days as clearly they are key weapons for the future. You will have no awareness if there is zero days in any digital device you have or app you run until it is either discovered (through testing, patching, intelligence or the zero day being used in an attack elsewhere) or until it is used on you.
Logic bombs - in the cold war the Russians had sent operatives into Western Europe with weapons and communications equipment and planted them in the ground. In the movies these always extend to suitcase nukes as well. With a logic bomb, a 3rd party is entering your code and inserting a weapon, usually to be triggered later in the event of a war. When these go off, here’s the sort of thing that happens (these were not always pure logic bombs but indicate the effect):
225,000 people lose power in the middle of the night on a freezing cold night in Ukraine
The data of banks and companies are deleted in South Korea
The University of Cambridge ran a potential scenario last year whereby a logic bomb was inserted into a database used widely around the world. It gradually changed data in the database and changed the data held in backups. This led to people not trusting data or technology and caused a global recession of 6-12m. They estimate the damage to the economy from that one logic bomb would be $4.5 trillion to $15 trillion.
Data exploitation - one website claims that 20 billion records were breached in 2020 alone. There is a full list here of the attacks that took place that month. The Chinese are alleged to have stolen the data of 80% of Americans (and you can assume that percentage is similar in other Western nations) and are also gathering DNA on individuals. It’s almost certain that your records are already in a database of a 3rd party that has intent to exploit it at some point. What hit home to me on my course is we still talk a lot about not sharing too much online - that horse has largely bolted and we are now trying to shut the stable door (which is still important). Here’s some recent examples of data breaches:
A customer support database holding with 280 million Microsoft customer records was left unprotected on the web
10.6m records from people who have stayed at MGM Resorts
0.5m Zoom account credentials for sale on the dark web
An unsecured database with 235m Instagram, Tiktok and YouTube profiles was found online
Scraped data of 500m LinkedIn users was being sold online this year
Canva - 137m records include name, email, city of residence, hashed passwords and partial credit card data
eBay 145m users
Marriott - 500m users information stolen
MySpace - 360m user accounts leaked
Yahoo - 3 billion user accounts - names, emails, phone numbers and dates of birth
What should we prepare for
It’s not that cyber warfare is coming - it’s already here. There is a difference between cyber war (all out attacks to support a hot kinetic war) and cyber warfare (sabotage, propoganda, espionage).
Here’s what you can anticipate:
More and more attacks on the most used services;
Increasing theft of any data you have online;
Ransom attacks on your employer, government, voluntary associations, public services and individually;
Deep fakes meaning you are watching video and media you think is real from a voice of influence in your life but is just computer generated;
State to state attacks that enable retaliation without hot wars (e.g. Natanz attack on the nuclear facility);
Greater confusion over the truth;
Disruption to infrastructure on a regular basis, particularly areas we rely on heavily - transport, power, healthcare, water systems.
Non state actors (e.g. organised crime or hacking groups) being used as proxies for state attacks (Russia is know to already do this)
How can we prepare
You basically can’t. I have seen estimate that the US has 100 people in cyber offense for every 1 in cyber defense. When I wrote an essay (catchingly titled “A profile of the cybersecurity strategy and threat environment of the United States”) for my course, there were at least 62 separate agencies responsible for cyber security in the US. Even with the creation of Cyber Command, there is a focus on offense rather than defense.
As an organisation you could know your data, test your vulnerabilities, have a backup - but any of those could be taken out by a logic bomb. One of the best methods of defense was always thought to be air gapping - i.e. you have a network or a device that is not connected to the Internet. But Stuxnet jumped one and blew up centrifuge devices.
As an individual you can limit your data online, use multi factor authentication, use an external service to check if your passwords and ID are available online (e.g. Breachwatch), delete old accounts on services you no longer use.
There’s a strong argument that you should become a digital prepper. In 2017 the Estonians decided to move a Soviet army statue. In response to this slight to Russia, the country was attacked for 22 days in one of the largest DDoS attacks ever. Cash machines didn’t work, online banking didn’t work, Government services didn’t work, newspapers and broadcasts were denied access to publish the news. This is a mere fraction of what all out cyber war would look like.
There’s only one solution. Don’t be completely reliant on technology. How would you and your organisation survive if the internet went down?
What I am reading
I started this a few days ago. I knew little of the East India Company other than it has a pretty horrific reputation. Imagined in 1599 and authorised in 1600, it was one of the first joint stock companies, without a closed group of shareholders. It wasn’t the first company - that honour went to the magnificently named “The Mysterie and Companie of the Merchant Adventurers for the Discoverie of Regions, Dominions, Islands and Places Unknown”. I was once told by Robert Cook, ex CEO of Malmaison Hotels & the Hotel du Vin chain, that you should never give a company three names as it will immediately be abbreviated. I assume this was not an issue in the 16th century.
The East India Company was a response by English merchants who had seen the Dutch secure great riches, and in the process destroy the future of the Levant Company. Therefore they petitioned the Queen for permission to form this company. As with many tech companies today, it received significant incentives from the public purse including no customs duties for six years and a monopoly over trade to the “East Indies” (East of the Cape of Good Hope (S Africa) to the Straits of Magellan (Chile)) - or effectively almost half of the world. The authorisation granted permission to rule territories and raise armies. Interpreted by the East India Company, they later claimed jurisdiction over all English subjects in Asia, minted money, built castles and fort, made laws, waged war, developed foreign policy, sent people to prison and founded towns. By 1803, it had 200,000 men in its army and had conquered the Eastern half of India.
My great grandparents on my mother’s side apparently owned a coffee plantation in India. I have seen one photo of them in India but I know little of the back story. My grandfather was born in India - I once investigated whether I was eligible to play football (soccer) for India but it turns out not as he was born before India declared independence from the British Empire. I was told that he was sent back from India to boarding school in Edinburgh when he was 7 and never saw his mother again. It’s strange to think that if the East India Company had not been founded, he may never have even set foot in India.
The East India Company is a part of British history that we don’t like to talk about. For good reason. Even without being selective or revisionist, there is much to be appalled by. This book does a good job of telling the history - from the 218 men who founded it (as permissioned by one woman) to the 19th century when its vision was largely realised.
This week marked the one year anniversary of The Weekly Distillation. With over 14,000 opens, 41 newsletters and an average email open rate of 68%, I’m grateful for the engagement and encouragement. Here’s some of the feedback I’ve had:
“You’ve a way with words blended with an educated balanced insight too.”
“I honestly really enjoy reading these. They’re interesting first off. However, you’ve a way with words that’s cuts to the chase wrapped up in a soothe sarcastic undertone. Bravo I say.”
“Excellent stuff. Fascinating. Provoking"
“Mate, love the briefing!”
I plan to keep writing, hopefully you plan to keep reading! Sláinte










Great read for a Saturday morning! It really makes me think how I can secure my data d how to prepare my business if internet goes down.